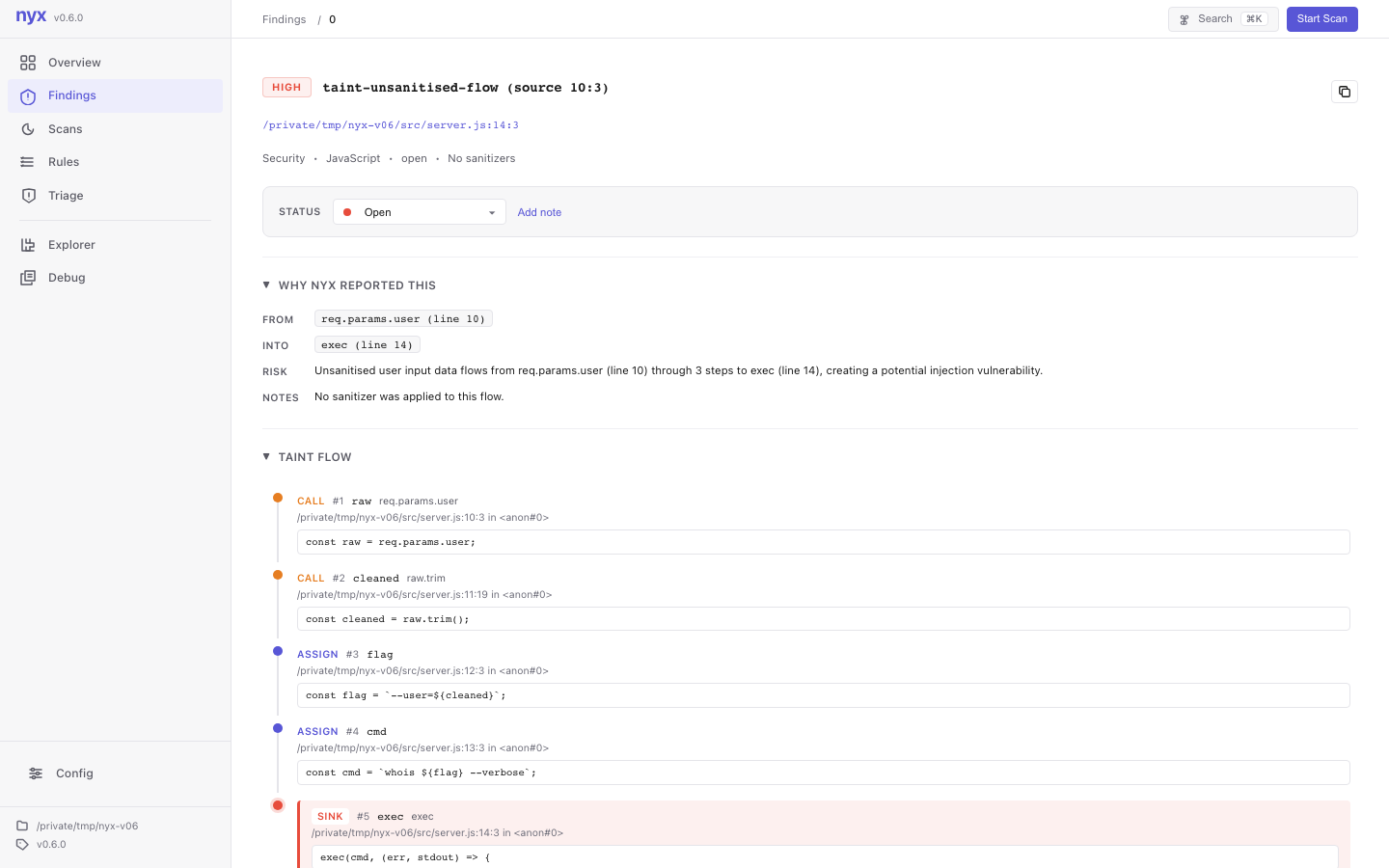
What changed
The new taint-data-exfiltration rule fires when sensitive data reaches the body, headers, or
JSON payload of an outbound HTTP request. Cookie, header, environment, file, database, and caught
exception sources are treated as sensitive. Plain user input is filtered out at emission time, because a
proxy passing a request body upstream is usually not the thing worth yelling about.
The sinks cover the common request clients across JavaScript, TypeScript, Python, Java, Go, Rust, Ruby,
PHP, C, and C++. SARIF output also records which outbound field carried the leak, such as
body, headers, or json.
Noise controls
There are a few practical knobs: sanitizer names for analytics and metrics wrappers, a trusted destination allowlist, and a detector toggle for teams that want to leave the rest of taint analysis on while disabling this class.
Other fixes in this build
- Ruby SSRF coverage now includes
OpenURI.open_uri. - Lodash
_.templateis modeled as a gated code-execution sink. - Helper-validation summaries can carry validated parameters through return values.
- Rust web-framework auth checks gained better typed-extractor handling.
Release Notes for today's update can be found here.